Documentation

Introduction
QueryPie AIP Introduction
Everything You Need to Know About QueryPie AIP
Manuals
QueryPie ACP Community Edition Installation Guide
QueryPie ACP Community Edition is a free version that lets you experience all the core features of QueryPie ACP Enterprise — including Database, System, Kubernetes, and Web Access Controllers — with a maximum limit of 5 users. Get started quickly with a simple installation.

Blogs
AI Security Threat Map 2026 | 7 Attack Vectors and Practical Defense Framework for CxOs
AI security is not an extension of traditional cybersecurity—it requires an additional defense layer. Explore 7 AI-specific attack vectors including prompt injection and model supply chain threats, with an OWASP and NIST-aligned governance framework for CxOs.
March 3, 2026
![[2026 Update] The Full Scope of Shadow AI Risk: 5 CxO Actions to Prevent Data Leaks and Compliance Violations](/documentation/blogs/b-thumb-27.webp)
Blogs
[2026 Update] The Full Scope of Shadow AI Risk: 5 CxO Actions to Prevent Data Leaks and Compliance Violations
Shadow AI is now a board-level business risk. IBM reports that breaches linked to shadow AI cost an average of $4.63M. This article explains five concrete actions for CxOs to prevent data leakage, compliance failures, and NDA violations, backed by the latest data.
February 20, 2026
Blogs
テラスカイ社のMCP対応AIプラットフォーム 「mitoco Buddy」が正式ローンチ
QueryPie AI合同会社は、株式会社テラスカイが提供する、企業向けMCP対応AIプラットフォーム「mitoco Buddy」が、このたび正式にローンチされたことをお知らせいたします。
December 23, 2025
Blogs
QueryPie AI、株式会社テラスカイと協業しAIエージェント「mitoco Buddy」を発表
QueryPie AI合同会社(本社:東京都港区、共同代表:Brant Hwang、以下「QueryPie AI」)は、株式会社テラスカイ(本社:東京都中央区、代表取締役CEO 社長執行役員:佐藤 秀哉、以下「テラスカイ」)と、AIエージェント事業分野において協業することを発表しました。本協業により、QueryPie AIのエンタープライズ向けAIプラットフォーム「QueryPie AI Platform(AIP)」が、テラスカイの新サービス「mitoco Buddy」に採用され、企業内に乱立するクラウドサービスを統合し、情報連携およびデータ活用を促進することで、意思決定の加速化と業務自動化を支援します。
November 7, 2025

Blogs
Top 10 Privileged Access Management (PAM) Solutions You Should Know
Discover the top 10 Privileged Access Management (PAM) solutions that are essential for modern enterprise security, featuring comprehensive leading platforms that provide advanced credential management, zero-trust access control, and automated security features to protect your organization's critical IT infrastructure in today's rapidly evolving digital landscape.
August 11, 2025

Blogs
株式会社ペイロールとQueryPieがAIセキュリティ分野で技術提携
株式会社ペイロール(本社:東京都江東区、代表取締役社長:湯浅 哲哉、以下「ペイロール」)と、統合データガバナンスプラットフォームを提供するQueryPie, Inc.(本社:米国カリフォルニア州、CEO:Brant Hwang)およびその日本法人であるQueryPie Japan合同会社(本社:東京都港区、代表:有延 敬三、以下「QueryPie」)は、AIとセキュリティ分野における技術提携に合意したことをお知らせいたします。
August 5, 2025

Blogs
How Much Can We Trust AI? The Naked Truth of AI Agent Security Through the Replit Incident
The incident where Replit AI Agent deleted a production DB is not just a technical mistake, but highlights the importance of security architecture when deploying AI agents in real environments. This case summarizes a security checklist including AI hallucination detection, least privilege design, and execution log retention.
July 29, 2025
Blogs
AI Rebels Are Becoming Reality — Why We Need AI Red Teaming
AI is no longer just generating answers — it’s executing real-world actions. Through real incidents and case studies, QueryPie explains emerging AI security threats like command refusal and indirect prompt injection, and why AI Red Teaming is now essential.
June 10, 2025
Blogs
Next.js Server Action and Frontend Security
Next.js Server Actions' high-level abstractions may lead developers to make security mistakes. This article analyzes these risks and presents development strategies to prevent security errors. Enhance your security awareness when developing server-side code in the frontend to build safer and more efficient web applications!
March 20, 2025

Blogs
Cost Optimization through EC2 Automation: Leveraging AWS Lambda and EventBridge
Learn how to optimize EC2 costs by automating instances with AWS Lambda and EventBridge. This guide explores best practices for cost reduction through serverless solutions.
February 7, 2025

Blogs
Why is SSO important?
Understand why Single Sign-On (SSO) is crucial for enhancing user experience, streamlining access, and improving security across multiple platforms. See the benefits today!
February 4, 2025

Blogs
Demystifying Privileged Access Management: Insights, Comparisons, and Practical Applications
Discover how PAM strengthens security by managing and monitoring privileged access, reducing risks to critical data.
January 23, 2025

Blogs
Healthcare Data Security: Protecting Patient Privacy and Ensuring Compliance
Discover how to safeguard healthcare data with advanced security measures, ensuring patient privacy, compliance, and protection from data breaches. Learn more now!
January 17, 2025

Blogs
Zero Trust Security: Redefining Cybersecurity in a Hyper-Connected World
Understand how Zero Trust Security can protect your business by continuously verifying users, devices, and networks, ensuring stronger defense against threats. Explore it now!
January 16, 2025

Blogs
Mastering Data Observability: Insights, Techniques, and Best Practices
Understand QueryPie's commitment to an agentless approach for streamlined and secure system management.
January 9, 2025
Blogs
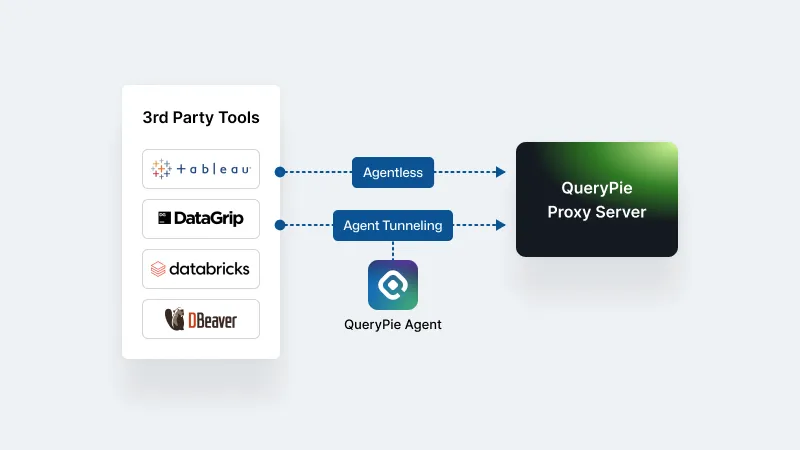
Why QueryPie Stands Firm on Its Agentless Philosophy
Understand QueryPie's commitment to an agentless approach for streamlined and secure system management.
November 22, 2024
Blogs
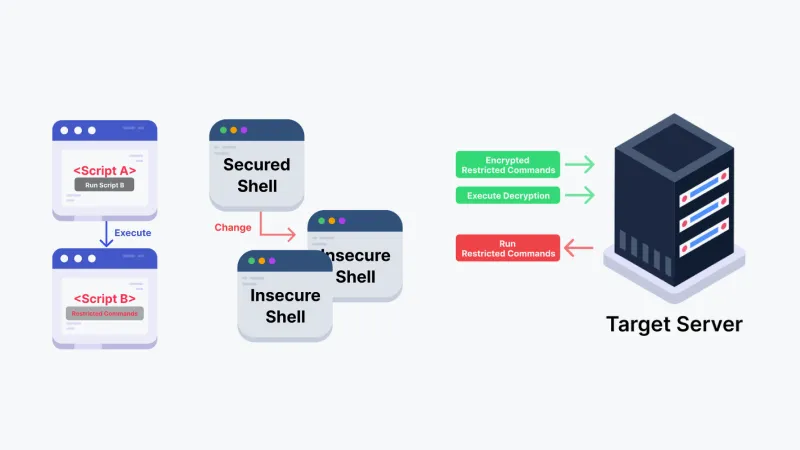
The Overlooked Command Bypass Issue: Let’s Finally Talk About It!
Addressing the overlooked risks of command bypass issues and how QueryPie offers advanced solutions to prevent them.
November 22, 2024

Blogs
A Peek Into a Day in the Life of QueryPie TPM Team: The Secret to Winning Over Customers
A glimpse into QueryPie TPM's daily efforts to win customer trust and deliver exceptional results with effective strategies.
November 22, 2024

Blogs
Your New Ally in Data Privacy and Management: Data Discovery
Learn how QueryPie's data discovery tools enhance privacy management and ensure compliance with global data regulations.
November 22, 2024

Blogs
QueryPie’s New Paradigm: Beyond Integration, Toward True Connectivity
QueryPie introduces a new paradigm, emphasizing true connectivity beyond mere system integration for better collaboration.
November 22, 2024

Blogs
Data Leaks: How a Small Internal Breach Can Turn into a Disaster
Explore how small internal breaches can escalate into major data leaks and how QueryPie helps mitigate risks effectively.
November 22, 2024

Blogs
From Chaos to Order: Revolutionizing Multi-Cloud Kubernetes Access Control
QueryPie's approach to streamlining multi-cloud Kubernetes access control for enhanced security and operational efficiency.
November 22, 2024

Blogs
Cracking the Toughest Global Markets: What Makes QueryPie So Confident?
How QueryPie confidently tackles global market challenges with innovative solutions and strategic expertise.
November 22, 2024
Blogs
QueryPie PM’s Work Smarts: Transforming into a True All-Rounder
QueryPie PM insights on becoming an all-rounder through effective work strategies and cross-functional collaboration.
November 22, 2024

Blogs
Secrets of Successful Teams? Work Like QueryPie!
Explore QueryPie's secrets to building successful teams through collaboration and shared values.
November 22, 2024
Blogs
QueryPie x Figma: The Ultimate Guide to Seamless Collaboration
Discover how QueryPie and Figma ensure seamless collaboration for design and development teams, boosting productivity.
November 22, 2024

Blogs
QueryPie’s Stride & Sustainability by Converging Technology and Humanities
How QueryPie merges technology with humanities to drive innovation and ensure long-term sustainability.
November 22, 2024

Blogs
What businesses can learn from Sentiment Analysis
Learn how sentiment analysis can boost your business by understanding customer emotions, refining strategies, and enhancing satisfaction. Explore its power today!
April 26, 2022

Blogs
AI Attack Tools Breach 600 Firewalls Across 55 Countries: How to Protect the Data Beyond the Firewall
An AI-powered open-source attack platform breached 600+ FortiGate firewalls across 55 countries. An unskilled threat actor leveraged AI to execute attacks at scale. This article analyzes the CyberStrikeAI incident and presents a defense-in-depth framework for CxOs to protect data beyond the firewall.
March 9, 2026
Glossary
QueryPie AI Glossary - Key Terms and Definitions
Access QueryPie AI's glossary of key terms related to data governance and security. Learn essential terminology for understanding our platform and the industry.
White Papers
The End of SaaS, or Its Evolution? — Strategies SaaS Companies Must Adopt in the Age of AI Agents
This white paper analyzes the impact of AI agents on the SaaS business, outlines the strategies SaaS companies should adopt, and shares the real story of QueryPie AI's transformation from a SaaS vendor to an AI-native company.

White Papers
Guardrail Design in the AI Agent Era (2026 Edition) — Part 1: Philosophy & Design
As AI agents move from conversational assistants to autonomous executors, enterprises need stronger control systems. This 2026 guide explains a four-element guardrail framework—Permission, Approval, Audit Trail, and Kill Switch—for CxOs and operational leaders.

White Papers
Guardrail Design in the AI Agent Era (2026 Edition) — Part 2: Practice & Implementation
A practical implementation guide for AI-agent guardrails. Includes three case studies (PC-operation agents, development AI vulnerabilities, and autonomous 5G operations), a reusable checklist, and a 90-day rollout roadmap.
White Papers
コード生成およびAgentic RAGタスクを中心とした特定ドメインのためのLLM比較評価【前編】
LLMのベンチマークを信じないでください。ドメインに最適化されたLLMを自ら評価・選定しましょう。日本の給与システムの実パイプラインを対象に、13のLLM構成を体系的に比較評価した研究の前編です。
White Papers
コード生成およびAgentic RAGタスクを中心とした特定ドメインのためのLLM比較評価【後編】
13のLLM構成による実験結果を徹底分析。Thinkingモードの意外な落とし穴、GPTの安定性問題、そして60%のコスト削減を実現する最適パイプライン構成を明らかにします。

White Papers
Why Japanese Enterprises Are Accelerating Their AI Transformation Now
A concise, executive guide that diagnoses Japan’s AI gaps and delivers a pragmatic roadmap to turn AI into enterprise-wide productivity and growth.
White Papers
Your Architecture vs. AI Agents: Can MCP Hold the Line?
In this article, we clearly distinguish the roles of the MCP server and AI agents, providing a structured explanation of their respective responsibilities and limitations to prevent misunderstandings.

White Papers
Welcome to the Age of AgentSecOps—Code Stands Still, Agents Take Over
As AI agent–based automation systems continue to proliferate, we’ve moved beyond simple task automation to a new paradigm: AgentOps, where autonomous agents make decisions and interact with external systems on their own. In this article, we explore the emerging concept of AgentSecOps—security operations tailored for agent-driven environments—and take a deep dive into how its structure and role compare to traditional DevSecOps frameworks.
White Papers
Beyond MCP to MCPS: The Need for a Secure Protocol for Enterprise AI
MCP(Model Context Protocol) is innovative, but it has a critical weakness for use in enterprise environments. In this article, we will look at the basic concepts and current status of MCP, and deeply analyze the security issues that arise in enterprise environments.
White Papers
Google Agentspace Gets Things Done—QueryPie MCP PAM Keeps Them Safe
Google Agentspace is a powerful AI execution platform, but unchecked automation raises security concerns. This post explores how QueryPie MCP PAM enables secure, policy-based control for enterprise-grade AI adoption.

White Papers
Uncovering MCP Security: Threat Mapping and Vulnerability Analysis through Literature-based Investigation
As AI systems become increasingly interconnected, context sharing between models is critical to ensure reliable reasoning and secure execution. This white paper analyzes recent research on the Model Context Protocol (MCP), identifies key security threats, and proposes a next-generation architecture—MCP PAM—for context-aware access control and autonomous policy enforcement.
White Papers
AI Can Drive Itself—Why Not Secure Itself? Introducing Autonomous Access Control
In an era where AI directly executes system operations, traditional security models are no longer enough. This white paper introduces a new security paradigm for MCP-based AI execution environments—QueryPie MCP PAM—and outlines strategic approaches to achieving Autonomous Access Control.
White Papers
MCP PAM as the Next Step Beyond Guardrails
As generative AI adoption accelerates, traditional guardrails fall short in securing real-world LLM integrations. This whitepaper explores how MCP-based Privileged Access Management (PAM) complements existing safeguards to enforce user-intent-aware, context-driven control over AI operations—addressing threats like prompt injection, insider abuse, and sensitive data leakage.
White Papers
Security Governance and Integrated PAM Strategy for AI Agents in the Age of the Model Context Protocol (MCP)
Learn how integrating Privileged Access Management (PAM) into the Model Context Protocol (MCP) framework strengthens AI governance, enhances visibility, and mitigates emerging security risks in enterprise environments.
White Papers
Secure Server Access in an Era of Network Isolation: Multi-hop Bidirectional Tunneling via the SSH Protocol
As enterprises adopt network isolation, secure access to internal servers becomes more complex. This white paper outlines the limitations of traditional SSH methods and explains how QueryPie enables seamless, scalable server access through multi-hop tunneling and centralized control—without exposing intermediate credentials.
White Papers
Optimal Method for Using a Terminal with Seamless SSH Connection
Discover an optimal method for seamless SSH connections that enhances security without disrupting the CLI workflow. Learn how QueryPie’s approach eliminates the need for additional agents while maintaining robust access control.
White Papers
QueryPie gRPC DAST Security: ZAP Custom Script Example
Learn how QueryPie leverages gRPC communication for high performance and stability in web applications.

White Papers
Efficient Storage and Management of Large-Scale Audit Logs (OVEN)
Guiding efficient storage and management of large-scale audit logs while meeting security and compliance requirements.

White Papers
Access Control for Secure Operation of Kubernetes Clusters
QueryPie ensures secure Kubernetes access control for improved cloud cluster management and operational security.
White Papers
Revolutionizing Security Management with Policy as Code (PaC)
Automate and optimize security protocols using QueryPie's Policy as Code, ensuring compliance and reducing risks.
White Papers
Core Technology for Parsing SQL Across Multiple Vendors: QSI (Query Structural Interface)
Enhance system security with QueryPie's native command control through an advanced SSH proxy architecture.

White Papers
QueryPie’s New Standard for Penetration Testing
QueryPie sets a new benchmark in penetration testing to prevent vulnerabilities and secure systems effectively.
White Papers
Improving Personal Data Identification and Analysis with AI
Utilize QueryPie's AI to analyze personal data, ensuring better privacy management and regulatory compliance.

White Papers
Preventing Command Bypass at the Source with Process-Tracking Methods
Prevent command bypass threats at the source with QueryPie's innovative process-tracking methods.

White Papers
QueryPie’s DevSecOps Pipeline: Proven to Enhance Development Speed and Stability
Streamline development with QueryPie's DevSecOps pipeline for enhanced speed, stability, and security.

White Papers
Secure Login Token Management: An Essential Frontend Strategy
Secure user authentication with QueryPie's login token management, enhancing frontend security and data protection.
White Papers
Shell Native Command Control through SSH Proxy Architecture
Enhance system security with QueryPie's native command control through an advanced SSH proxy architecture.
White Papers
Building a Transaction-Free, Flawless CDC (Change Data Capture) System
Sync data seamlessly with QueryPie's CDC system, ensuring conflict-free updates without transactions.

White Papers
RAG 2.0 Security: Microsoft and Meta’s Groundwork, QueryPie Builds the Bridge
This article introduces the background and security architecture of RAG 2.0 and emphasizes the importance of execution flow control through various corporate cases. RAG 2.0 is differentiated from existing RAGs in that it goes beyond simple document search and applies policies in real time to prevent sensitive information from being delivered to the wrong users.
Stop Thinking.
Start Transforming.
Sign up in seconds and secure your 14-day free trial now.